HYPERAUTOMATION
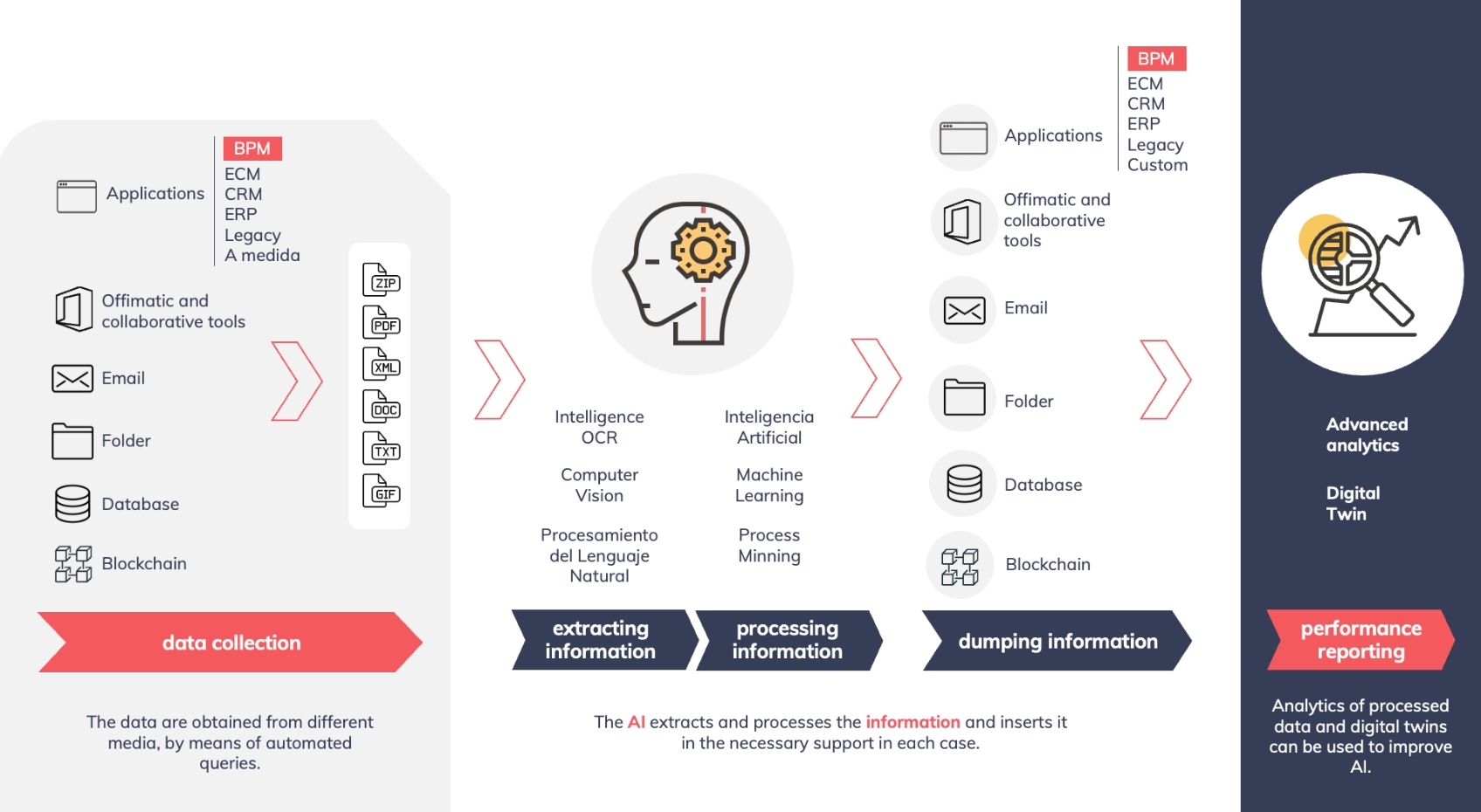
Hyper-automation starts with robotic process automation (RPA) at its core and extends automation capability with disruptive technologies such as AI, machine learning (ML), process mining and natural language processing (NLP), and can go further with the integration of other technologies such as blockchain or computer vision.
Our difference
EXPERIENCE
Extensive experience in consultancy work in different sectors and development of complex projects based on a diverse technology stack (RPA, BPM, AI, ML, etc.) based on best practices and implementation methodologies.
CUSTOMER ORIENTATION
Continuous search for solutions adapted to customer business processes, based on robots and solutions that combine other enabling technologies to build efficient and high-impact use cases.
GLOBAL SOLUTION
Izertis brings its extensive knowledge in the deployment of technological integration projects of great complexity and variety of technologies to build hyper-automation solutions in an agile and global way.
HYPERAUTOMATION IN A NUTSHELL
OUR SERVICES
CONSULTANCY
- Process re-engineering
- Process assessment and elaboration of the hyper-automation strategy roadmap
- Identification of suitable tools and architecture for hyper-automation
- Hyper-automation strategy implementation and governance models
- Definition of framework and best practices
CENTRE OF EXCELLENCE
- Proof of concept (PoC) development
- Configuration of the implementation model
- Implementation of hyper-automation projects
- Centre of Excellence configuration
- Change management and end-user training
- Implementation support (software maintenance and licence management) Continuous improvement
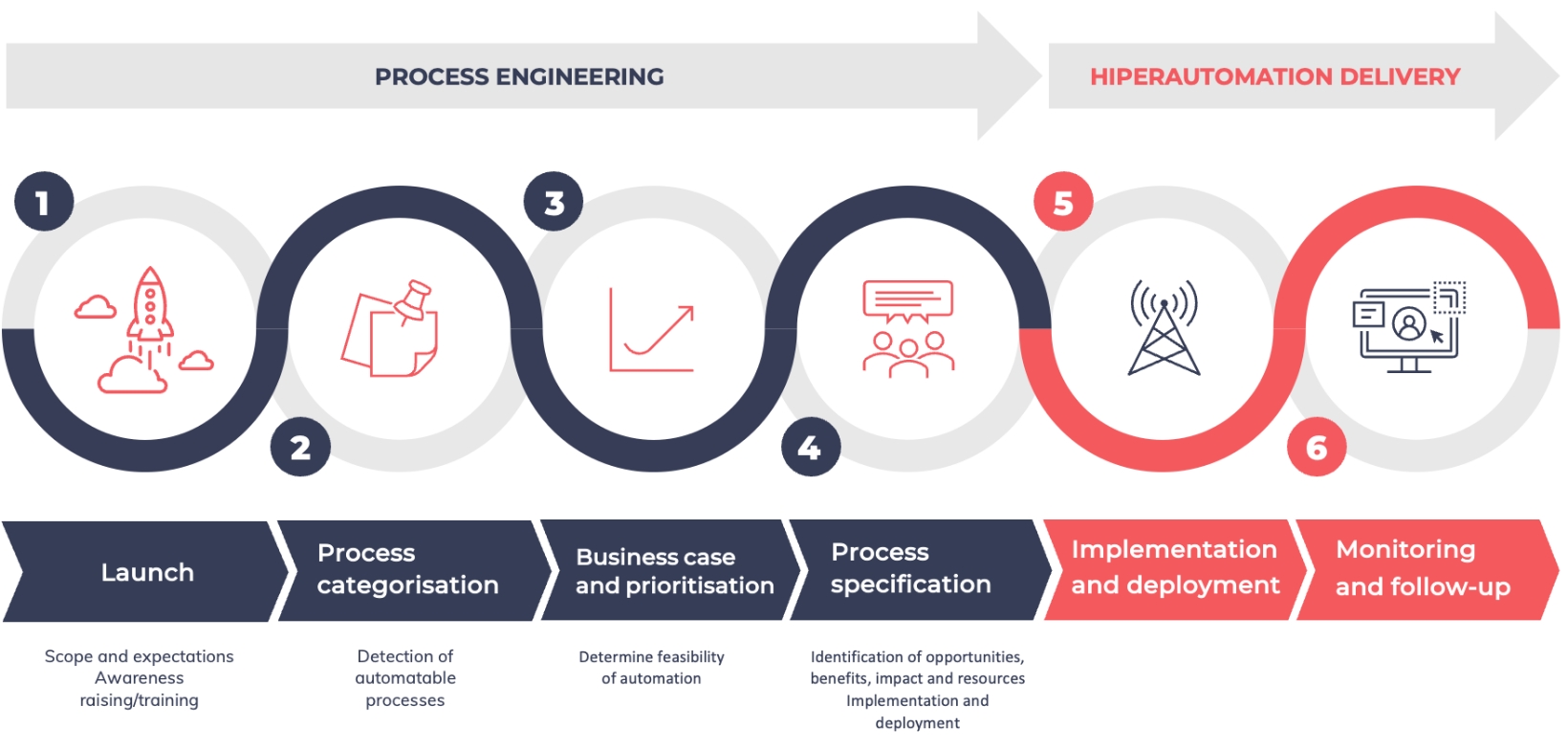
OUR SERVICE DEPLOYMENT FRAMEWORK

OUR ENABLING TECHNOLOGIES
RPA
OUR ENABLING TECHNOLOGIES
SENSORIZATION
BLOCKCHAIN
CONVERSATIONAL ASSISTANTS
BLOCKCHAIN
JOIN THE SECOND DIGITAL REVOLUTION

Use Blockchain in a simple way with our solutions adapted to your needs, both On Premise and Saas.
SIMPLIFICATION
We avoid the technological complexity of configuration and deployment.
SAVING
We avoid the costs of maintaining and updating the technological architecture.
SECURITY
Participation in the Blockchain requires identification, authentication and authorisation.
PRIVACY
We avoid the technological complexity of configuration and deployment.
CONFIDENTIALITY
We avoid the costs of maintaining and updating the technological architecture.
INTEGRATION
Participation in the Blockchain requires identification, authentication and authorisation.

